Kód: 04832030
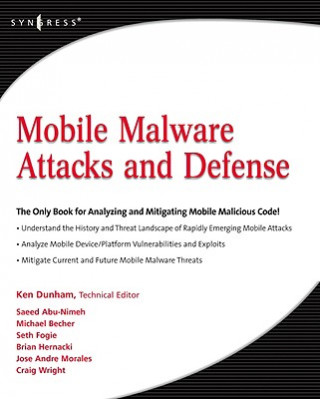
Mobile Malware Attacks and Defense
Autor Ken Dunham
Malware has gone mobile, and the security landscape is changing quickly with emerging attacks on cell phones, PDAs, and other mobile devices. This first book on the growing threat covers a wide range of malware targeting operating ... celý popis
- Jazyk:
 Angličtina
Angličtina - Vazba: Brožovaná
- Počet stran: 440
Nakladatelství: Syngress Media,U.S., 2008
- Více informací o knize

Mohlo by se vám také líbit
-
Attachments
303 Kč -

Small Business Solutions
481 Kč -

Deer
973 Kč -

Freud's Paranoid Quest
2884 Kč
Darujte tuto knihu ještě dnes
- Objednejte knihu a zvolte Zaslat jako dárek.
- Obratem obdržíte darovací poukaz na knihu, který můžete ihned předat obdarovanému.
- Knihu zašleme na adresu obdarovaného, o nic se nestaráte.
Více informací o knize Mobile Malware Attacks and Defense
Nákupem získáte 160 bodů
 Anotace knihy
Anotace knihy
Malware has gone mobile, and the security landscape is changing quickly with emerging attacks on cell phones, PDAs, and other mobile devices. This first book on the growing threat covers a wide range of malware targeting operating systems like Symbian and new devices like the iPhone. Examining code in past, current, and future risks, protect your banking, auctioning, and other activities performed on mobile devices. Visual Payloads - view attacks as visible to the end user, including notation of variants. Timeline of Mobile Hoaxes and Threats - understand the history of major attacks and horizon for emerging threats. Overview of Mobile Malware Families - identify and understand groups of mobile malicious code and their variations. Taxonomy of Mobile Malware - bring order to known samples based on infection, distribution, and payload strategies. Phishing, SMishing, and Vishing Attacks - detect and mitigate phone-based phishing (vishing) and SMS phishing (SMishing) techniques. Operating System and Device Vulnerabilities - analyze unique OS security issues and examine offensive mobile device threats. Analyze Mobile Malware - design a sandbox for dynamic software analysis and use MobileSandbox to analyze mobile malware. Forensic Analysis of Mobile Malware - conduct forensic analysis of mobile devices and learn key differences in mobile forensics. Debugging and Disassembling Mobile Malware - use IDA and other tools to reverse-engineer samples of malicious code for analysis. Mobile Malware Mitigation Measures - qualify risk, understand threats to mobile assets, defend against attacks, and remediate incidents. Understand the history and threat landscape of rapidly emerging mobile attacks. Analyze mobile device/platform vulnerabilities and exploits. Mitigate current and future mobile malware threats.
 Parametry knihy
Parametry knihy
Zařazení knihy Knihy v angličtině Computing & information technology Computer networking & communications Network security
1599 Kč
- Plný název: Mobile Malware Attacks and Defense
- Autor: Ken Dunham
- Jazyk:
 Angličtina
Angličtina - Vazba: Brožovaná
- Počet stran: 440
- EAN: 9781597492980
- ISBN: 1597492981
- ID: 04832030
- Nakladatelství: Syngress Media,U.S.
- Hmotnost: 918 g
- Rozměry: 234 × 192 × 19 mm
- Datum vydání: 12. November 2008
Oblíbené z jiného soudku
-
Web Application Hacker's Handbook: Finding and Exploiting Security Flaws 2e
1031 Kč -
Ghost in the Wires
459 Kč -
Hacker Playbook
720 Kč -
Nmap Network Scanning
1007 Kč -
How to Speak Tech
713 Kč -
Google Cloud Certified Professional Cloud Network Engineer Guide
1421 Kč -

Blue Team Handbook
519 Kč -

Wireshark 101
1560 Kč -

GSEC GIAC Security Essentials Certification All-in-One Exam Guide, Second Edition
1317 Kč -

Wireshark Certified Network Analyst Exam Prep Guide (Second Edition)
1223 Kč -

Stealing the Network: The Complete Series Collector's Edition, Final Chapter, and DVD
2138 Kč -

Foundations Of Information Security
913 Kč -
Python Ethical Hacking from Scratch
1126 Kč -
Countering Cyberterrorism
6048 Kč -

Metasploit
1134 Kč -

Practical Packet Analysis, 3e
1174 Kč -

UTM Security with Fortinet
1797 Kč -
Practice Of Network Security Monitoring
1291 Kč -
CISSP Practice Exams, Fifth Edition
704 Kč -

Learning Kali Linux
1523 Kč -

PowerShell and Python Together
910 Kč -
Tangled Web
1249 Kč -

Network Security Through Data Analysis
1378 Kč -
Computer Forensics and Digital Investigation with EnCase Forensic v7
1078 Kč -
Advanced Persistent Threat Hacking
1160 Kč -
Cisco ISE for BYOD and Secure Unified Access
1926 Kč -
Cisco ASA for Accidental Administrators
1169 Kč -
Zero Trust Networks
1166 Kč -
VMware vSphere Essentials
1370 Kč -

Industrial Network Security
1733 Kč -

Wireshark Network Analysis (Second Edition)
3232 Kč -

Network Forensics
1985 Kč -

Kali Linux Cookbook
1288 Kč -
Rootkit Arsenal: Escape and Evasion in the Dark Corners of the System
3253 Kč -
Quantum Key Distribution Networks
3289 Kč -

Cisco ASA Configuration
1512 Kč -

Applied Network Security Monitoring
1456 Kč -
Kali Linux - Assuring Security by Penetration Testing
1370 Kč -

IPv6 Security
1747 Kč -
Wireshark for Security Professionals - Using Wireshark and the Metasploit Framework
1066 Kč -

Security Power Tools
1378 Kč -

Learning Network Forensics
1532 Kč -

Information Assurance Handbook: Effective Computer Security and Risk Management Strategies
1512 Kč -
Configuring Juniper Networks NetScreen and SSG Firewalls
1133 Kč -
Dawn of the Code War
413 Kč -
Mobile Application Hacker's Handbook
1750 Kč -

Comptia Security+
964 Kč -
IoT Hacker's Handbook
1189 Kč -

Network Security with OpenSSL
928 Kč
Osobní odběr Praha, Brno a 12903 dalších
Copyright ©2008-24 nejlevnejsi-knihy.cz Všechna práva vyhrazenaSoukromíCookies



 Vrácení do měsíce
Vrácení do měsíce 571 999 099 (8-15.30h)
571 999 099 (8-15.30h)